
The Colonial Pipeline Ransomware Attack: How to Beat Ransomware with a CDP Approach
This week the Colonial Pipeline, a 5,500 mile pipeline that supplies upwards of 45% of the gasoline delivered to the east coast of the United States, was brought to an unprecedented halt due to a ransomware attack. The attack is hitting home for many U.S. consumers and causing political reverberations reaching all the way to the White House. As the attack stretches into its sixth day, gasoline panic buying has caused sharp shortages at gas stations in many states.
This attack highlights the vulnerability of the nation’s infrastructure to the growing threat of cyber-attacks and ransomware. Questions arise about protecting the critical and sometimes highly complex systems and applications that keep our day-to-day lives “always-on”. From the gas in our vehicles, to the electricity charging our devices, to the clean water we so easily take for granted, situations like the Colonial Pipeline attack are frightening reminders that ransomware is not just something we read about in the news.
Sadly, the threat of ransomware is only growing in complexity and scale, but the good news is that the data protection industry is outpacing attackers to combat these threats. There are is a multitude of approaches to protecting datacenters and applications, but the ultimate goal is to mitigate any downtime or disruption.
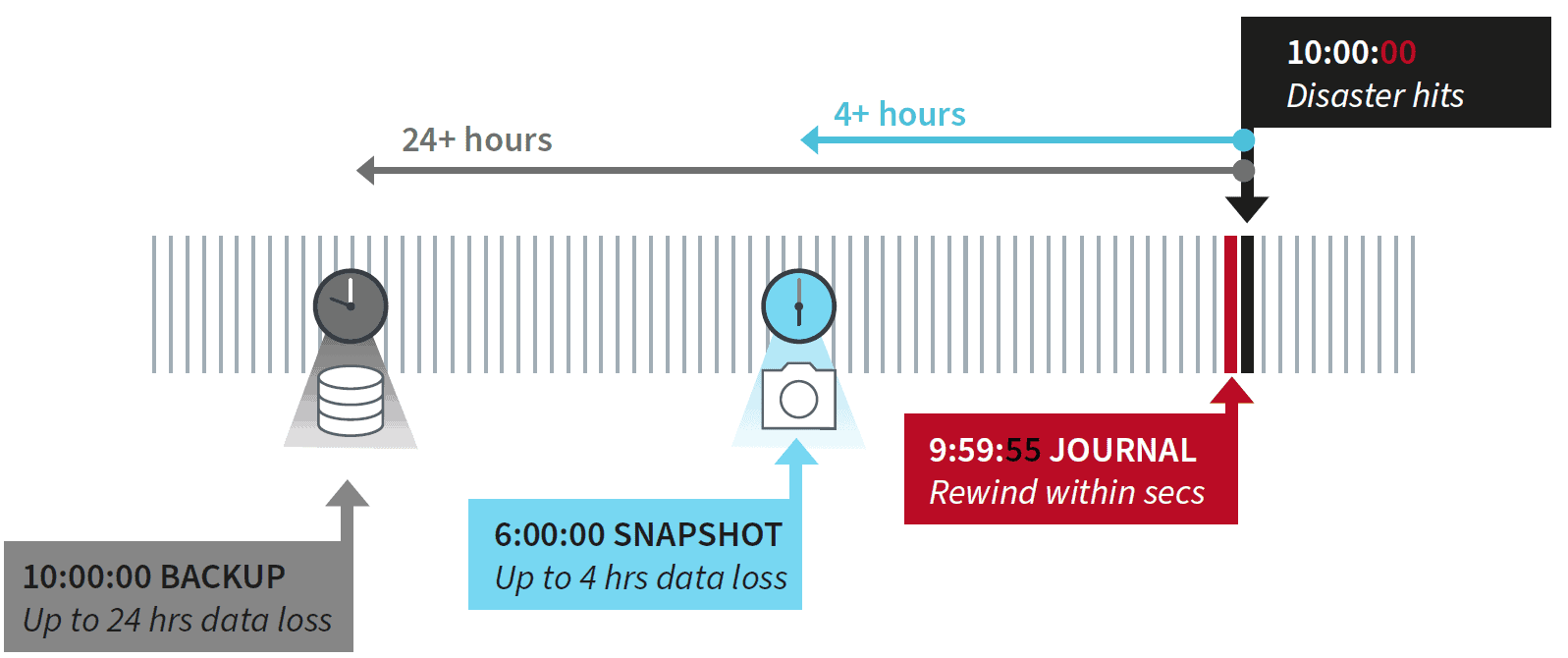
Traditional backup technologies sometimes rely on day-old or even week-old backups to restore their data. This results in inevitable protection gaps and data loss that can be highly disruptive and add significantly to the overall recovery cost. Nightly snapshots are an old-school approach that is not sustainable in a world where even minutes of downtime can be costly to both a company’s bottom line as well as its brand integrity.
The key is having a solution that’s always-on, with enough granularity to recover to a point in time precisely before the attack occurred. The best solution will be one that uses continuous data protection (CDP) and keeps valuable data protected in real time.
Critical infrastructure is being targeted more often, so the organizations that oversee these systems need to rethink their approach to recovery and resilience to deliver continuous data protection that allows organizations to replicate data as changes occur and then quickly recover without hours of data loss.
For more information on taking a modern CDP-forward approach to data protection, download this IDC Technology Spotlight report: “Continuous Data Protection: A New Era of Backup and Recovery”
UPDATE 5/14/21
 Carley Oberdoerster
Carley Oberdoerster 

