Managing Cyberthreats to Combat Ransomware Part 1: Current Technologies
Ransomware has been at the top of headlines for several years now, and we have either heard or experienced first-hand the pain it can cause. While the prevalence of ransomware is still growing and a very real threat for the foreseeable future, we can’t forget the other cyberthreats lurking at the doorstep that could pave the way for a ransomware disaster.
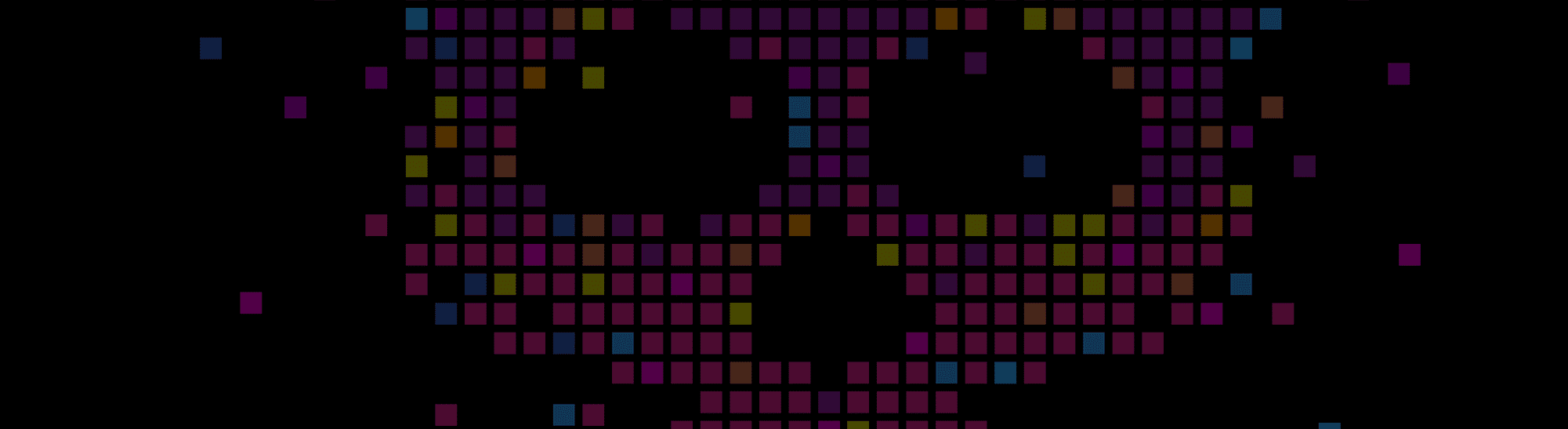
According to the Center for Internet Security over the past six months (DEC 2021–MAY 2022), these ten malware variants consistently made up over 60% of all reported malware activity:
- Shlayer
- ZeuS
- Agent Tesla
- Arechclient2
- NanoCore
- CoinMiner
- Gh0st
- Delf
- RedLine
- Jupyter
These malware variants can exfiltrate sensitive data, compromise credentials, and deploy unwanted software—all which on their own are detrimental and can even lead to further compromise such as ransomware.
So how to do you protect your organization? Is there a silver bullet or a magical box that protects all your systems and data from every threat? Well, I’m sorry to inform you, regardless of what you may have heard lately, the answer is no. To best understand how to protect your organization, let’s start with the basics.
What is cybersecurity?
Cybersecurity is the practice of protecting data, systems, networks, applications, and programs from digital attacks. Cyberattacks usually entail accessing, changing, or destroying sensitive information, extorting money from organizations and users, as well as interrupting normal business operations.
Implementing effective cybersecurity measures is challenging today because there are more devices than people, and bad actors are becoming more innovative in initiating and deploying cyberattacks. A cybersecurity program requires educating and hiring the right people, implementing proven processes and frameworks, and deploying the proper technology layers to prevent and mitigate threats.
The Most Common Cyberthreats
With the cyberthreat landscape so vast, new types of malicious software and bad actors are emerging every day to compromise organizations and individuals. There are numerous ways cyberattacks may occur. Understanding some of the more common ways a compromise can happen will better equip you to handle these threats. Below are some of the most common cyberthreats.
1. Ransomware
Ransomware is a type of malware that blocks access to a system, device, or file until a ransom is paid by the attack victim. This is achieved when the ransomware encrypts files on the infected system, threatens to erase files, or blocks system access for the victim. The ransom amount and contact information for the bad actor is typically included in a ransom note that appears on the victim’s screen after their files are locked or encrypted. Sometimes the bad actor only includes contact information in the note and will attempt to negotiate the ransom amount once they are contacted.
2. Social engineering
In a social engineering attack, a bad actor uses human interaction to obtain or compromise information about an organization or its computer systems. A bad actor may seem unassuming and respectable, possibly claiming to be a new employee, repair person, or researcher and may even offer credentials to support that identity. However, by asking questions, he or she may be able to piece together enough information to infiltrate an organization’s network. If a bad actor is not able to gather enough information from one source, they may contact another source within the same organization and rely on the information from the first source to add to their credibility.
3. Phishing
Phishing attacks use email or malicious websites to solicit personal information by posing as a trustworthy organization. For example, a bad actor may send email seemingly from a reputable credit card company or financial institution that requests account information, often suggesting that there is a problem. When users respond with the requested information, attackers can use it to gain access to the accounts.
4. Weak patch management
Many cyberattacks attempt to exploit outdated software first. Not staying up to date with software patches can leave companies vulnerable to information security breaches, and as soon as attackers learn of a software vulnerability, they can exploit it to launch a cyberattack. Patch management is the process of distributing and applying updates to software.
See other types of cyberattacks.
Common Technologies Used for Cybersecurity
Cybersecurity and data protection involve implementing the proper technologies, cyber security controls, and the adoption of good cyber practices to mitigate the risk of a compromise. Here are some of the most common and practical technologies your organization can implement to better prepare and mitigate the risk of compromise from a cyberattack.
1. Intrusion Detection System (IDS)
An IDS monitors inbound and outbound communications for unusual or unauthorized activities over various network communication protocols. If an unauthorized activity is detected, the intrusion detection logs are sent to a central logging facility or system where correlation and analysis will be accomplished as a system-wide intrusion detection effort such as a Security Information Event Management System (SIEM).
2. Intrusion Prevention System (IPS)
An IPS analyzes system and network behavior to detect and mitigate the use of various system commands or scripts that indicate malicious activity.
3. Anti-malware Software
Anti-malware software can be deployed to detect and remove various types of malware such as rootkits, worms, trojans, and others by scanning both incoming files and files in place.
4. Anti-Phishing Solutions
Anti-phishing solutions come in multiple forms, but one primary type examines incoming messages like email, SMS, and employs spam filters to try to identify phishing attempts. Other anti-phishing solutions help train users to avoid phishing attacks by sending out fake phishing messages to test if users engage with these simulated attacks.
5. Multi Factor Authentication (MFA)
MFA is an authentication system that requires a layered approach to securing data and applications by requiring a user to present two or more credential types to be granted access.
6. Data and Storage Immutability
Storage and Data Immutability, as its name would suggest, means that the data, once written cannot be modified or deleted. Immutability is one of the best defenses against malware that can modify or encrypt data, as well as accidental deletion of data.
7. Security Information Event Management System (SIEM)
A SIEM is a log analytics platform configured with security-relevant correlation alerts. This technology helps map events within applications and the underlying infrastructure to generate and deliver alerts to responsible stakeholders based on corresponding events and metrics.
Cybersecurity is Continuing to Evolve
By leveraging these types of technologies and implementing the proper training, most organizations can achieve a relatively robust protection level of cybersecurity. But cyberattacks are continuing to evolve, becoming more sophisticated and more disruptive with new technologies and strategies. Emerging technology combats some of these newly evolved threats like ransomware. In this continuing series of blog posts on cybersecurity, we’ll delve deeper into some of these technologies to combat cyberattacks and how they fit into cybersecurity frameworks your organization should be following to stay vigilant against growing threats.
Stay tuned for part 2 of this three-blog series on how to manage cyber threats. In the meantime, check out how Zerto can help you Get out of Ransomware Jail.
 Andrew Silva
Andrew Silva 
