Zerto Tip: Change Your PowerShell API Credentials
Quick tip for a little extra security with Zerto
Let me start by saying that by default unless you have your Windows firewall wide open, no one who doesn’t already have access to your Zerto server can access the PowerShell API. Zerto listens for PowerShell requests on port 9080 by default and that port is normally blocked by the Windows firewall.
However, if you do need to execute Zerto PowerShell commands remotely, you will need to open that port and because of that, I recommend changing the default administrator password and/or adding a new user with a custom password.
Where are credentials stored?
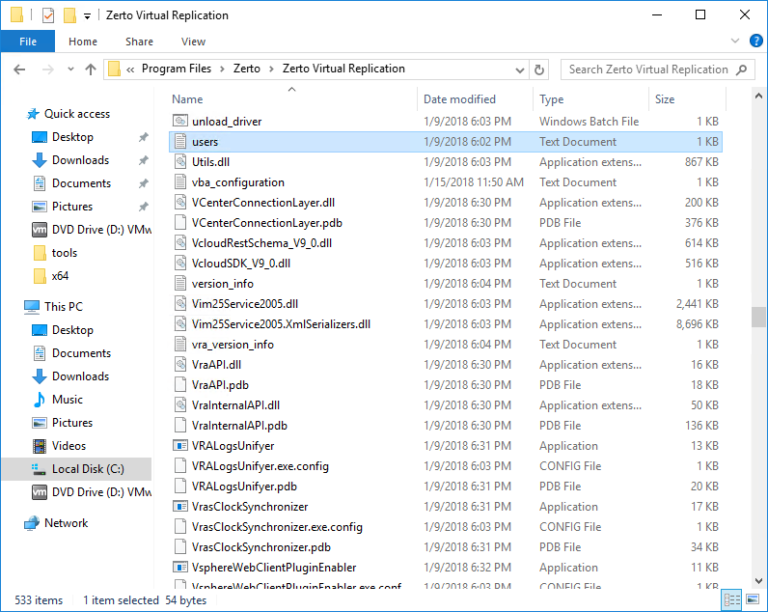
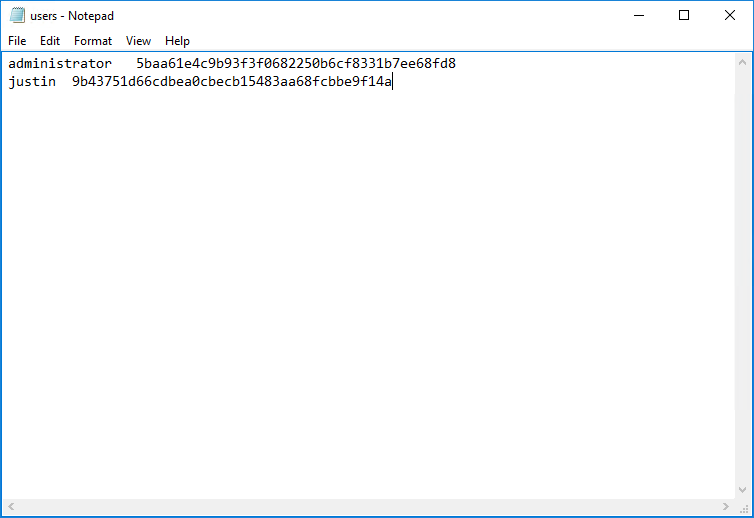
If you login to your Zerto Virtual Manager via the console or RDP then navigate to the Zerto’s Virtual Replication installation folder (default path is c:\Program Files\Zerto Virtual Replication) you will find a “users.txt” file.
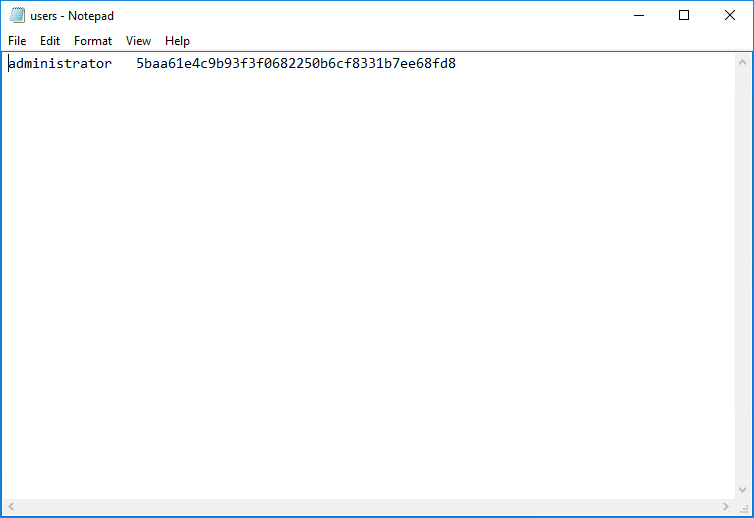
Open up the users.txt file. By default the only user is “administrator” with a password of “password”, the password is stored as a sha1 hash.
How can I change the password for the administrator user account?
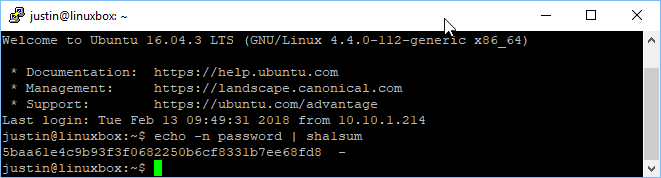
All you need to do is delete the current sha1 hash and replace it with a hash of the password you want to use. There are a couple ways to do this if you have a Linux machine close by you can generate a sha1 has by using the following command: echo -n password | sha1sum
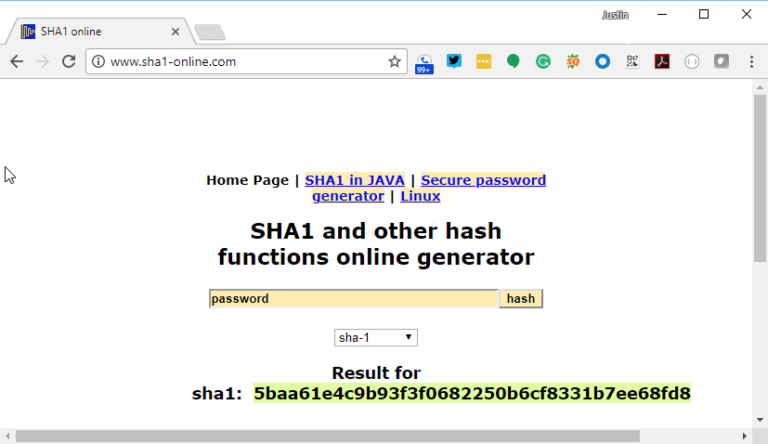
If you aren’t a Linux user, there are also some online generators that will create the sha1 hash for a given string. I don’t know how secure they are, but honestly, to become an issue they would need to breach your corporate firewall, find your ZVM IP, know the PowerShell API port and then have knowledge of the Zerto PowerShell API… So I feel pretty safe using http://www.sha1-online.com/ but just know that if you want NSA level security … get a Linux box that isn’t connected to the network.
Regardless of how you get your sha1 hash, you just need to paste it into the users.txt file and save the file. No need to restart ZVM, as the changes take effect immediately.
Can I add a different user?
Yes! All you need to do is add a new line with the username followed by then the sha1 hash value. If you want to remove the administrator user altogether and just have a custom username that is also possible.
Hope this helps and thanks for reading! See the original post on Justin’s IT Blog here.
 Justin Paul
Justin Paul
Justin is a Technical Alliances Architect for Zerto. He also specializes in all things virtualization, storage, and servers. When not helping people learn about protecting their data from disasters, he is usually working on stuff in his home lab or spending time with his family.