GDPR is Coming… Are You Ready?
What is the GDPR?
The General Data Protection Regulation (GDPR) is a new law that is intended to strengthen and harmonise the data protection rights of individuals within the European Union (EU), but it also addresses the export of any personal data to countries outside the EU. The GDPR is much broader and stricter than ’the 1995 EU Data Protection Directive, which it will replace. The GDPR was adopted in 2016 and will come into force on May 25, 2018.
Why should I care about the GDPR?
GDPR applies not only to businesses located in the EU, but also to businesses that offer goods and services to, or otherwise monitor, individuals located in the EU. This means that businesses with no operations in the EU may still need to operate according to the GDPR’s requirements. It is likely also that governments of countries outside the EU will implement similar laws. The GDPR will be enforced by data protection authorities, and failure to comply with its terms can lead to fines up to a whopping 4% of annual global turnover or €20.000.000 (whichever one is higher).
Okay okay.. you have got my attention! How can Zerto help?
Let’s start with the GDPR’s definition of a personal data breach:
‘personal data breach’ means a breach of security leading to the accidental or unlawful destruction, loss, alteration, unauthorised disclosure of, or access to, personal data transmitted, stored or otherwise processed;
As you can see, even accidental deletion or facing a ransomware attack can lead to organisations having to report a breach. When reading through the regulation it states, multiple times, that businesses have to take “appropirate technical measures” to comply, however it does not mention anything about the “how” or what is considered “appropriate”. Instead, this depends on the data processing taking place, and the risks posed by that personal data. Now let’s take a closer look to the article that discusses the security of processing (article 32) and how we can help;
Security of processing
Taking into account the state of the art, the costs of implementation and the nature, scope, context and purposes of processing as well as the risk of varying likelihood and severity for the rights and freedoms of natural persons, the controller and the processor shall implement appropriate technical and organisational measures to ensure a level of security appropriate to the risk, including inter alia as appropriate:
(a) the pseudonymisation and encryption of personal data; 4.5.2016 L 119/51 Official Journal of the European Union EN
Due to Zerto’s technology agnostic approach we are transparent to any type of network, storage or guest -based encryption method giving you the freedom to choose the solutions that best meet your requirements.
(b) the ability to ensure the ongoing confidentiality, integrity, availability and resilience of processing systems and services;
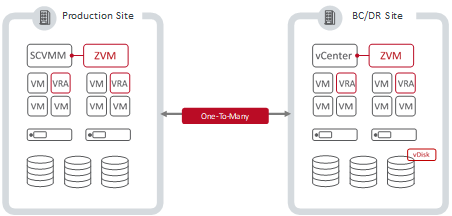
Zerto provides Continuous Data Protection (CDP) that ensures the write-order fidelity of multi-VM applications with near-zero data loss, guaranteeing the integrity of replicated data. Seamless data mobility and infrastructure flexibility, across both on-premises and cloud environments, enables organizations to not only maximize the availability of, but also ensure the ongoing resilience of processing systems and services in the face of increasing threats and constant change.
(c) the ability to restore the availability and access to personal data in a timely manner in the event of a physical or technical incident;
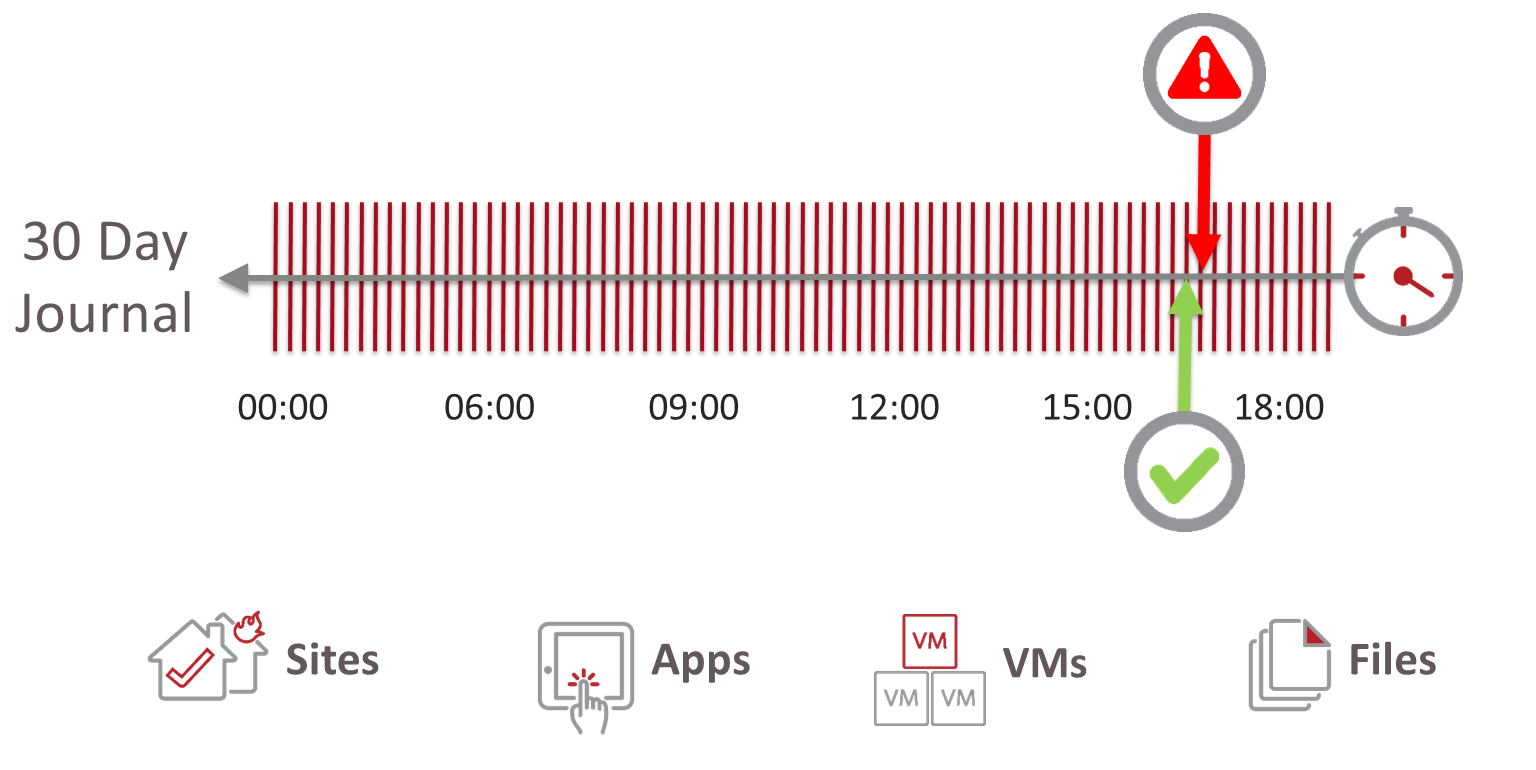
We provide Recovery Point Objectives (RPOs) of seconds & Recovery Time Objectives (RTOs) of minutes, with fully automated & orchestrated recovery of even complex, multi-VM application stacks. Rewind & recover from any physical or technical incident – even ransomware – with just 4 simple steps, choosing from potentially thousands of recovery points in increments of seconds for up to 30 days in the past.
(d) a process for regularly testing, assessing and evaluating the effectiveness of technical and organisational measures for ensuring the security of the processing.
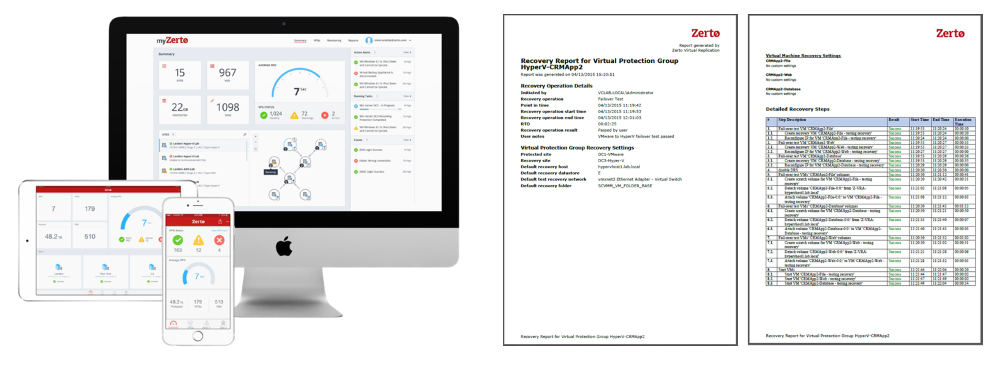
Zerto’s IT Resilience platform provides fully automated, non-disruptive and granular failover testing in isolated bubble networks for recovery assurance, with detailed reporting functionality to document proof of compliance during audits and inspections. A single person can test recovery operations in minutes with just 4 simple steps, without impacting protection and any impact or disruption to production workloads. We offer a consistent user experience across any type of technology by providing an easy to use Management GUI, Mobile App and webbased analytics portal with SLA driven dashboards that provide you with a quick overview of the health of your environment and allows you use long term reporting for SLA reporting, protection environment sizing and/or trend analysis.
The ability to test the recovery process combined with reporting (both on recovery and SLA) is very important as it is required to prove compliance (see articles: 24 & 28).
But wait there is more….
Chapter V of the GDPR sets out rules relating to international transfers of personal data. The European Commission can find that a third country provides an adequate level of protection for personal data, allowing personal data to be transferred there legally. If a country that you want to transfer personal data to is not “adequate”, extra steps have to be taken before the transfer can take place.
Besides protecting your data, Zerto also offers great mobility capabilities allowing you to migrate applications and data in minutes across any distance. This allows you to act in a timely and controlled fashion when data residency rules change. Our great global Cloud Service Provider eco-system, consisting of more than 350 providers, also allows you to select an organisation that best fit your needs regrading compliance and data residency.
Closing remarks.
Although there is never a single solution to suit all needs for regulatory compliance, organizations can use Zerto to greatly assist in ensuring compliance with a wide variety of regulations at industry, regional & international levels, including the GDPR.
Please note that this blog post contains only a summary of relevant laws and is not intended to amount to legal advice on which you should rely. You should obtain your own, independent legal advice in relation to your organisation’s compliance with applicable laws.
Interested in learning more? Register now for our GDPR webinar on January 18 at 11:00am ET.